How to Decrypt Kazu Ransomware (.kazu) Files Safely?
A Kazu incident doesn’t always begin with encrypted files; it often starts when an organization learns—sometimes from the dark web, sometimes from the news—that their name has appeared on a Kazu leak site or Telegram channel. In other cases, internal teams discover suspicious access, strange data transfers, or extortion emails claiming that critical information has been stolen. Not long after, the organization finds itself listed alongside government agencies, law-enforcement portals, education ministries, humanitarian groups, insurance providers, job portals, and healthcare entities from around the world.
Victims have included names like Leadway Assurance (Nigeria), CT Dent Ltd (UK), multiple Colombian, Venezuelan, Mexican, Sri Lankan, Emirati, Thai, Bolivian, and Argentinian public-sector platforms, as well as job portals and social-service agencies. This victim list paints a clear picture: Kazu is not a small nuisance; it is a rapidly expanding extortion and data-broker operation that targets high-value, data-rich organizations in both the public and private sectors.
Unlike classic encrypt-and-lock ransomware families, Kazu often functions as a data exfiltration and extortion group: it infiltrates systems, steals sensitive files, and then uses leak sites and communication channels (such as its Tor portal and Telegram handle) to pressure victims into paying.
However, even when the threat actors claim to hold hundreds of gigabytes of sensitive information, victims are not powerless. With structured incident response, forensic analysis, and disciplined communication, organizations can respond effectively without caving to ransom demands.
At the center of that structured response is Kazu Decryptor, our dedicated data-extortion and ransomware response platform designed to analyze Kazu incidents, map stolen data, assess risk, and guide safe recovery and hardening—without paying extortion.
Related article: How to Decrypt .cod Files After Cod Ransomware Attack?
Regain Stability With Our Kazu Decryptor
The Kazu extortion playbook follows a familiar pattern seen in modern data-broker ransomware operations:
- First, access is gained and data is quietly exfiltrated.
- Then the group contacts the victim or posts them on their Tor leak site or Telegram channel.
- Finally, Kazu threatens to leak or sell the data unless payment is made by a specific deadline.
In many Kazu posts, the group claims to hold large volumes of internal documents, databases containing personally identifiable information (PII), law-enforcement records, social-service records, job seeker data, healthcare data, and sensitive government material. Government portals and critical public-service systems are heavily represented in their victim listings, including civil-service employment systems, human-rights institutions, police and military portals, education ministries, social-security agencies, and municipal services.
The key tactic isn’t always encryption—it’s exposure.
Kazu often leverages double extortion: threatening both operational disruption and publication of sensitive data.
Kazu Decryptor is built to counter exactly this model. Even if the group has stolen data (and even when encryption hasn’t occurred), organizations need:
- precise visibility into what data is likely in attacker hands,
- clarity on the exposure across sectors, users, and jurisdictions,
- calm guidance on how to respond without overreacting or underreporting.
Kazu Decryptor supports this by tying together incident telemetry, leak-site monitoring, and forensic analysis to give you a stable framework for decision-making.
Also read: How to Remove Cracker (Beast) Ransomware and Recover .cracker Files?
How Kazu Decryptor Supports Recovery & Response?
Because Kazu incidents often revolve around stolen data and publication threats rather than just encrypted endpoints, the recovery challenge is different from traditional ransomware. You’re not just dealing with locked files; you’re dealing with potential data exposure, reputational risk, and regulatory impact.
Kazu Decryptor provides a structured way to handle all of that:
- It aggregates intelligence from Kazu’s Tor site, Telegram announcements, and third-party leak-tracking platforms.
- It ingests sample data sets that Kazu may have posted or shared as “proof” to confirm that the leak is genuine and determine which systems are affected.
- It maps leaked samples back to your internal systems—job portals, insurance platforms, law-enforcement systems, social-service systems, healthcare databases, etc.—to identify exactly which users, records, and departments are impacted.
- It reconstructs a timeline by correlating logs (VPN, application, firewall, database, identity) with observed exfiltration behavior and extortion posts.
- It generates a clear exposure profile you can use for decision-making, regulatory reporting, and communication strategy.
Instead of acting on vague fear, you act on concrete, analyzed data—what Kazu has, how critical it is, and who it affects.
Step-by-Step Kazu Extortion & Data Leak Recovery Guide With Kazu Decryptor
Assess the Situation
Start by confirming that Kazu is actually involved. That may mean:
- discovering your organization’s name on a Kazu leak portal,
- seeing it mentioned in Kazu’s Telegram channel,
- or receiving direct extortion messages referencing Kazu infrastructure, timelines, or specific data volumes.
Identify the victim context: are you seeing a pure data leak threat, or evidence of both data theft and internal encryption? Some Kazu-related incidents may involve ransomware payloads; others are strictly data-broker style.
Stabilize & Contain
Immediately lock down access. Rotate credentials that may be exposed (VPN, privileged accounts, identity providers, service accounts used by critical portals, and database access). Limit access to affected applications while forensic work begins. Ensure no current attacker sessions are active and that no backdoors are left in place.
Engage Our Recovery & IR Team
Provide:
- any extortion emails or messages received,
- screenshots or text copies of Kazu leak-site posts mentioning your organization,
- any sample files or data fragments Kazu has posted as proof,
- and logs from affected systems.
We use this to confirm authenticity of the threat, map which systems correspond to which leaked elements, and determine whether Kazu obtained live access (e.g., RDP, VPN, web app access) or exploited a vulnerable service.
Use Kazu Decryptor to Build Your Exposure & Remediation Profile
Our platform analyzes the samples Kazu has posted or claimed to possess and correlates them with your internal databases, document repositories, file servers, and SaaS systems. From there, we build a profile that answers:
- What categories of data were exposed (PII, HR data, health records, insurance records, law-enforcement data, job-seeker data, etc.)?
- Which geography and regulatory regimes apply (e.g., multiple Latin American countries, UAE, Nigeria, EU).
- Which systems need immediate hardening or rebuilds?
- Which users, departments, and third parties must be notified?
Execute a Coordinated Response Plan
Armed with a clear profile, you can make decisions grounded in reality:
- whether and how to notify affected individuals,
- what to disclose to regulators,
- how to structure communication to media and stakeholders,
- what sequence of technical remediation steps to follow.
Kazu Decryptor and our incident-response team help you plan and prioritize these tasks while keeping risk and compliance in focus.
Also read: How to Remove Coinbase Cartel (.cbcl) Ransomware From Windows & Servers?
What You Should Do If You’ve Been Targeted by Kazu?
The initial shock of seeing your organization named on a Kazu leak portal—or receiving a direct extortion message—can be intense. But your next actions are crucial.
Do not:
- rush into paying or contacting the extortion contact channels,
- start deleting systems, files, or logs out of fear,
- make public statements before you know what was actually exposed,
- assume that all claims about data volumes are accurate.
Instead:
- preserve all evidence of communication and postings,
- collect logs, event traces, and configuration backups for affected systems,
- coordinate internally with IT/security, legal, communications, and leadership,
- engage professionals who understand Kazu’s behavior, infrastructure, and tactics.
You cannot erase the fact that an attack occurred, but you can control the quality of your response.
Kazu Data Exposure & Reputation Recovery
Unlike strictly encrypting ransomware, Kazu focuses on stolen data. That means “recovery” is not about decrypting locked files—it’s about:
- limiting how widely the stolen data spreads,
- monitoring subsequent reposts or sales,
- mitigating regulatory and legal risk,
- reassuring stakeholders with accurate information and action.
Kazu Decryptor helps you:
- monitor Kazu’s infrastructure for new leaks involving your name,
- track whether partial or full dumps have been published,
- determine whether Kazu is selling access or full databases to third parties,
- and align your long-term risk posture accordingly.
Legacy, pre-incident backups do not “unleak” data, but they do allow you to rebuild systems in a hardened, controlled way, ensuring attackers cannot reenter easily.
Targets: Governments, Law Enforcement, Education, Healthcare, Social Services & More
Based on Kazu’s victim listings and independent threat reporting, the group has targeted a wide variety of organizations, including:
- national police forces and law-enforcement platforms (e.g., Nepal Police, Royal Thai Police),
- government ministries and portals (e.g., Mexico, Colombia, Sri Lanka, Saudi Arabia, Kuwait, UAE),
- education ministries and regional secretariats,
- humanitarian and social-service agencies (e.g., Guatemala DIF equivalents, Emirates Red Crescent),
- insurance and health-sector providers (e.g., Leadway Assurance, Vidal Health),
- job portals and employment platforms (e.g., Mexico’s job portal, Argentine job platforms, Iranian job sites),
- municipal and state-level digital services across Latin America.
This spread indicates that Kazu is not industry-specific; its unifying theme is data-rich systems with weak or uneven security.
Communicating During a Kazu Incident
Because Kazu often claims to have stolen sensitive data, communication must be handled with exceptional care.
Internally, staff should:
- be made aware that a data-extortion incident has occurred,
- be instructed not to discuss details externally,
- report any suspicious emails, calls, or follow-on phishing activity,
- and avoid speculation about data contents until confirmed.
Externally, organizations must:
- avoid prematurely confirming or denying specific data leaks before forensic validation,
- work closely with legal and compliance teams to craft notifications where required,
- provide factual, time-bounded updates rather than emotional reactions,
- emphasize steps being taken: containment, investigation, and mitigation.
A thoughtful communication strategy minimizes reputational harm and supports legal defensibility.
Long-Term Hardening & Prevention Against Kazu
Kazu attacks demonstrate the vulnerability of public-facing platforms and data-intensive systems. To reduce future risk, organizations should adopt:
- strong identity management (MFA, password hygiene, conditional access),
- continuous patching and vulnerability remediation for exposed web applications,
- network segmentation to limit the blast radius of breached accounts,
- strict access control and logging around critical portals (police, social security, health, education, insurance, employment),
- behavioral monitoring for anomalous exports, downloads, or administrator actions,
- and rigorous backup and disaster-recovery testing.
Most critically, organizations must train staff—especially those with privileged access or access to sensitive platforms—to recognize phishing, credential theft attempts, and social engineering.
Victim Analytics & Threat Trends for Kazu
Kazu Ransomware – Country Impact Distribution

Kazu Ransomware – Sector Impact Distribution

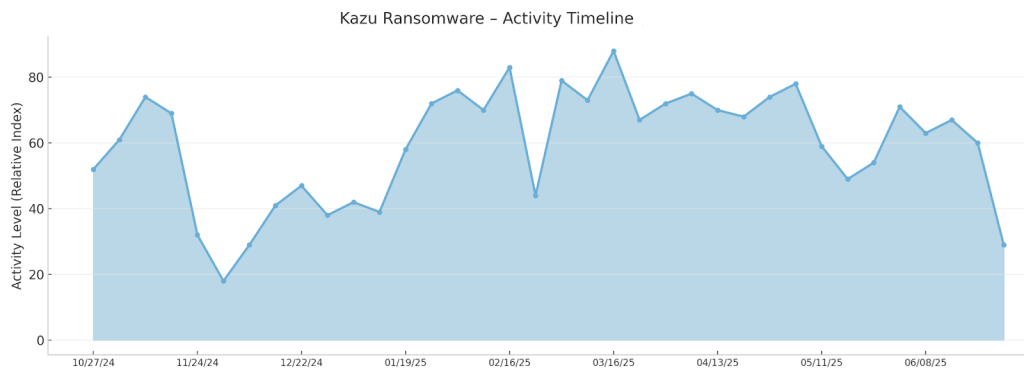
Kazu Ransomware – Activity Timeline
Technical Deep Dive: Kazu Data-Extortion & Ransomware Behavior
While Kazu is frequently grouped under “ransomware,” many of its incidents appear to focus on stealing and monetizing data, sometimes accompanied by system disruption. WatchGuard and AhnLab both describe Kazu as a data broker / ransomware and data-exfiltration group that relies on extortion rather than universal encryption campaigns.
Kazu maintains infrastructure that includes:
- a Tor hidden service (used as its primary leak site),
- a Telegram channel (e.g., t.me/kazu_breach) for announcements and victim naming,
- and back-end arrangements for storing and publishing stolen data sets.
Kazu Attack Lifecycle
1. Target Profiling & Reconnaissance
Kazu appears to focus on public-sector and highly regulated environments: ministries, civil-service platforms, police portals, educational systems, health providers, and humanitarian organizations. It likely identifies targets based on exposed web services, weak security posture, or known vulnerabilities in common platforms.
2. Initial Access
Initial access techniques vary, but are believed to include:
- phishing campaigns aimed at staff with administrative or portal access,
- exploitation of unpatched web applications or VPN appliances,
- use of stolen credentials obtained from other breaches or dark-web markets,
- and possible abuse of misconfigured cloud services.
These methods are consistent with other data-extortion operations across 2024–2025.
3. Privilege Escalation & Internal Mapping
Once inside, Kazu operators (or affiliates) work to escalate privileges, often moving from user-level accounts to administrative roles. They map out internal systems—databases, web portals, file servers, document management systems—and identify where sensitive data resides.
4. Data Discovery & Exfiltration
The primary goal is to extract high-value data: law-enforcement records, PII, medical and insurance records, employment and civil-service data, education records, and social-service data. Kazu may:
- query databases directly,
- export large record sets (CSV, SQL dumps),
- copy document repositories,
- and compress multi-gigabyte archives before exfiltration.
Network-level telemetry often shows sustained outbound transfers to servers not previously contacted.
5. Extortion Setup
After exfiltration, Kazu:
- compiles victim profiles,
- prepares data “proof” samples,
- and crafts messaging for direct contact or public listing.
At this point, they may either email the victim, post a teaser on Telegram, or publish a partial listing on the Tor leak site.
6. Extortion & Public Pressure
Kazu uses a mix of:
- direct extortion (private negotiation),
- double extortion (threatening data leaks),
- and occasional free data leaks to demonstrate capability or punish non-paying victims.
They may post a countdown or repeated updates warning that full data publication is imminent unless negotiations begin.
7. Data Sale & Reuse
If victims refuse to pay, Kazu may release part or all of the data publicly or sell it to third parties. Data can surface in other underground markets or be reused in follow-on fraud, identity theft, phishing, or credential stuffing.
Kazu Encryption Model (When Encryption Is Involved)
While much of Kazu’s activity is focused on data theft, some operations may also include traditional ransomware encryption within internal systems. In such cases:
- symmetric encryption (often AES or ChaCha20) may be used to encrypt files locally,
- keys may be protected by an asymmetric scheme (such as RSA),
- and file extensions, ransom notes, or on-disk markers identify Kazu as the actor.
However, because Kazu is primarily cataloged as a data broker / exfiltration-extortion group, encryption is not always observed and should not be assumed by default.
Key Indicators of Compromise (IOCs) for Kazu
Leak Site & Channel Indicators
- Tor domain used by Kazu for publishing victims and leaks.
- Telegram channel used for announcements and pressure.
Behavioral Indicators
- abnormal large-scale database exports,
- anomalous access patterns on government portals and job platforms,
- suspicious login attempts from foreign or previously unseen IP ranges,
- long-duration sessions with administrative privileges.
File & System Indicators (When Encryption Is Present)
- appearance of new ransom notes or changed wallpapers referencing Kazu,
- possible new extensions on encrypted files if Kazu uses a locker in specific incidents,
- deletion of shadow copies or log tampering.
These indicators vary by campaign and must be validated with forensic tooling.
Kazu Distribution Tactics
Kazu’s focus on high-value government and institutional targets suggests that:
- phishing emails tailored to public servants, law-enforcement staff, or system administrators are likely,
- exploitation of vulnerabilities in web frameworks, content management systems, or custom portals is probable,
- credential theft from prior breaches and underground data markets plays a role.
Evidence from threat reports indicates that Kazu is part of a broader trend of groups combining data theft, extortion, and occasional encryption rather than relying purely on crypto-locking.
Threat Summary: What Makes Kazu Dangerous?
Kazu is dangerous not because it encrypts every endpoint it touches, but because it:
- targets data-rich systems in sensitive sectors,
- exfiltrates large volumes of structured and unstructured data,
- uses multi-channel extortion (Tor, Telegram, direct contact),
- uses double extortion and free leaks to raise stakes,
- and undermines trust in critical public-service and private-service infrastructure.
It represents the data-centric evolution of ransomware operations, where damage extends beyond local file access to legal, reputational, and societal impact.
Conclusion — Structured Recovery Beats Extortion Pressure
Kazu’s strength is not in technology alone; it’s in exploiting fear. The group’s messaging, leak tactics, and victim selection are designed to push organizations into quick, quiet payments. But organizations that respond with structure, evidence, and expert guidance can come through a Kazu incident stronger than before.
With Kazu Decryptor and a disciplined response plan, you can:
- understand exactly what was taken,
- mitigate regulatory and legal risk,
- communicate responsibly,
- rebuild systems securely,
- and refuse to fund further criminal operations.
Recovery is not just about stopping a crisis; it’s about using that crisis to raise your resilience for the future.
Frequently Asked Questions
Contact Us To Purchase The Kazu Decryptor Tool






2 Comments