Marabu (.marabu) Ransomware Recovery and Removal Guide 2025
A new and dangerous ransomware family targeting Linux environments has been identified by security researchers. Named Marabu, this malware encrypts files and appends the .marabu extension, leaving behind a stark ransom note in a file named READ_THIS_NOTE.txt. As a Linux-based threat, Marabu represents a significant risk to enterprise servers, web hosts, and critical infrastructure.
This guide provides a comprehensive, step-by-step playbook for understanding the Marabu threat, containing the infection, and exploring every viable pathway to recover your systems and data without paying the ransom.
Related article: Lockis Ransomware (.lokis) GlobeImposter Recovery and Decryption Guide 2025
Threat Summary Table
| Attribute | Detail |
|---|---|
| Threat Name | Marabu Ransomware |
| Threat Type | Ransomware, Crypto Virus, Files Locker |
| Platform | Linux, Windows, ESXi |
| Encrypted Files Extension | .marabu |
| Ransom Demanding Message | READ_THIS_NOTE.txt |
| Free Decryptor Available? | No (As of this writing) |
| Ransom Amount | Varies, typically demanded in cryptocurrency. |
| Cyber Criminal Contact | Not specified in the provided note. |
| Detection Names | 360 Decryption Master: Not currently supported. Online Decryption: Not currently supported. |
Decoding the Threat: The Marabu Ransom Note
The Marabu ransomware uses a simple, direct text file to communicate its demands. The note is designed to be alarming and to immediately establish a sense of total loss and hopelessness.
The text presented in the ransom note reads as follows:
╔═════════════════════════════════════════════════════════════════════════════════════════════════╗ ║ ║ ║ ⚠️YOU LOST ALL YOUR FILES⚠️ ║ ║ ║ ╚═══════════════════ ════════════════════ ════════════════════ ════════════════════ ════════════════════╝ All your important files have been lost using a strong enc algorithm. To decr your files, write to us: ━━━━━━━━━━━━━━━━━━━━ ━━━━━━━━━━━━━━━━━━━━ ━━━━━━━━━━━━━━━━━━━━ ━━━━━━━━━━━━━━━━━━━━━
Also read: How to Recover Data from Ripper (.ripper12, .ripper20, .ripper32, MedusaLocker Ransomware?
Indicators of Compromise (IOCs) and Attack Behavior
Recognizing the signs of a Marabu infection on a Linux system is the first critical step. The malware’s distinct file extension and its target platform are its most obvious fingerprints.
Indicators of Compromise (IOCs):
- File Extension: The most obvious indicator is the appended
.marabuextension to all encrypted files (e.g.,database.sqlbecomesdatabase.sql.marabu). - Ransom Note File: The presence of a text file named
READ_THIS_NOTE.txtin directories containing encrypted files. - Platform: The infection is occurring on a Linux server or workstation, not a Windows machine.
- Process Names: The malicious executable may have a random or spoofed name (e.g.,
systemd,rsyslog). Look for unusual processes running with high CPU and disk I/O.
Tactics, Techniques, and Procedures (TTPs) with MITRE ATT&CK Framework:
- Initial Access (TA0001): Linux ransomware like Marabu often gains entry through exploiting unpatched vulnerabilities in web applications (e.g., WordPress, Joomla), poorly configured SSH services with weak or default credentials, or compromised third-party software repositories.
- Execution (TA0002): Once the attacker gains access, they execute a malicious script or binary that begins the encryption routine. This often runs with elevated privileges.
- Impact (TA0040): The primary impact is data encryption on Linux-based file systems, which can bring down web servers, application servers, and databases. The secondary impact is business disruption and potential data loss.
The Recovery Playbook: A Multi-Path Approach to Data Restoration
This core section outlines the primary methods for recovering your encrypted data from a Linux system.
Path 1: The Direct Decryption Solution
The most direct path to recovery is using a tool specifically designed to reverse the encryption.
Our Specialized Marabu Decryptor
Our team has developed a specialized decryptor to counter the Marabu threat. By leveraging advanced cryptographic analysis and pattern recognition, our tool can often reconstruct the decryption keys without needing to interact with the attackers.
Step-by-Step Guide:
- Step 1: Assess the Infection: Confirm that files have the
.marabuextension and verify the presence of theREAD_THIS_NOTE.txtfile on your Linux system. - Step 2: Secure the Environment: Disconnect the infected server from the network immediately to halt any further potential spread. It is critical to remove the malware from your system first.
- Step 3: Submit Files for Analysis: Send a few encrypted samples (under 5MB) and the ransom note file to our team. This allows us to confirm the Marabu variant and build an accurate recovery timeline.
- Step 4: Run the Marabu Decryptor: Launch the tool with administrative privileges (
sudo). The decryptor connects securely to our servers to analyze encryption markers and file headers. - Step 5: Enter the Victim ID: While the note does not provide a specific ID, our tool may generate a unique profile based on the file structures to begin the decryption process.
- Step 6: Automated File Restoration: Once initiated, the decryptor verifies file integrity and restores data automatically.
Also read: eCh0raix Ransomware Recovery Guide: Decrypt Your Synology NAS Files Without Paying
Public Decryption Tools and Repositories
If our tool is not applicable, several public initiatives are invaluable. Always identify the ransomware strain before using any tool, as running the wrong decryptor can cause permanent damage.
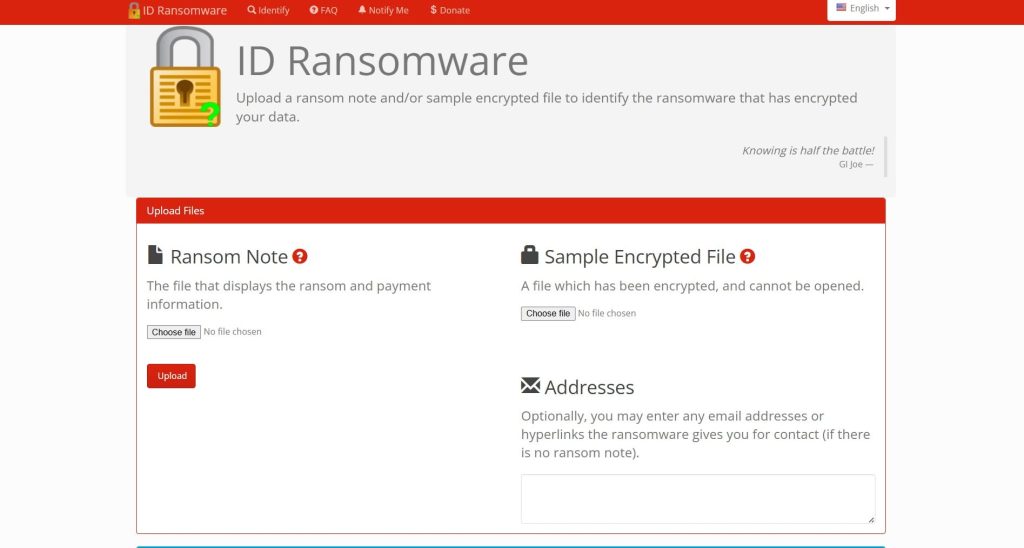
- ID Ransomware Service: Use the free ID Ransomware service to upload the ransom note and a sample encrypted file. The service will identify the strain and tell you if a known decryptor exists. Find it at ID Ransomware.
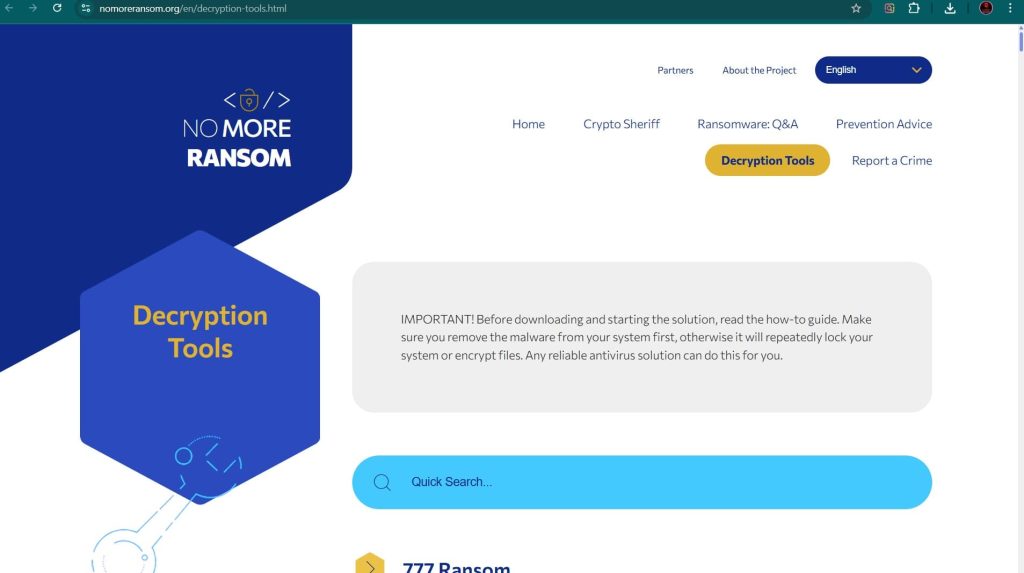
- The No More Ransom Project: This is the most important resource, providing a centralized repository of free decryption tools. Visit their Decryption Tools page and search for “Marabu”.
- Major Security Vendor Decryptors:
- Emsisoft: Renowned for its ransomware expertise, Emsisoft offers a variety of decryptors. Check their website for available tools at Emsisoft Decryptors.
- Kaspersky: Through its No Ransom portal, Kaspersky provides the latest decryptors and removal tools. Visit Kaspersky No Ransom.
- Avast: Provides numerous free ransomware decryption tools. Find them on the Avast Ransomware Decryption Tools page.
- Trend Micro: Offers a Ransomware File Decryptor for numerous known ransomware families. You can download it from the Trend Micro website.
Path 2: The Gold Standard – Backup Restoration
If a decryptor is unavailable, restoring from a backup is the most reliable method.
Enterprise-Grade Backups: Veeam
For businesses, Veeam is a market leader in backup and recovery solutions, offering robust protection for Linux environments. Veeam can create immutable backups that cannot be altered by the ransomware and offers specialized recovery processes like Cleanroom Recovery to prevent reinfection. Learn more at the official Veeam website.
Linux-Specific Backup and Recovery
- Rsync and Tar: For smaller setups, using
rsyncto sync data to an off-site location ortarto create compressed archives are common methods. If you have recentrsyncbackups ortararchives, you can restore from them. - Btrfs/ZFS Snapshots: If your file system is Btrfs or ZFS, you may have snapshots enabled. These are point-in-time, read-only copies of your file system that can be used to revert data to a state just minutes before the attack. This is often the fastest recovery method for file systems that support it.
- Cloud Backups: If you use a cloud backup solution like Bacula, Rclone, or a cloud provider’s native backup service, you can restore your files from there.
Path 3: Last Resort – Data Recovery Software
This method has a low probability of success with modern ransomware like Marabu but can be a lifeline if no backups exist.
- TestDisk & PhotoRec: These are powerful, free, and open-source data recovery utilities for Linux. TestDisk can recover lost partitions and repair boot sectors, while PhotoRec is designed to recover specific file types even if the file system is severely damaged. You can find them on the CGSecurity website.
- Foremost: Another console-based file recovery program that can recover files based on their headers, footers, and internal data structures. It is often included in Linux forensic toolkits.
- R-Linux: A commercial data recovery tool from R-Tools Technology specifically designed for the Linux file system (Ext2/3/4, ReiserFS, etc.). Find it at the R-Linux official site.
Important Procedure: For the best chance of success, you should shut down the affected server, remove its hard drive, and attach it as a secondary drive to a separate, clean Linux machine. Then, run the data recovery software on that clean machine to scan the secondary drive.
Essential Incident Response and Prevention for Linux
Recovery is only one part of the process. A full response includes containment, eradication, and future prevention.
Containment and Eradication
- Isolate the Infected System: Immediately disconnect the server from the network by unplugging the Ethernet cable or disabling the network interface (
sudo ip link set dev <interface> down). - Identify and Terminate the Malicious Process: Use commands like
ps auxortopto identify the process consuming high CPU/disk I/O. Terminate it withsudo kill -9 <PID>. - Remove the Malware: Locate and delete the malicious executable and the
READ_THIS_NOTE.txtfiles. Usefindto locate all instances of the note. - Change All Passwords: Assume all credentials are compromised. Change passwords for all user accounts, SSH keys, and root passwords. Also, change passwords for any services running on the server (databases, web applications, etc.).
Hardening Your Defenses with Modern Protection
The recommendations in the ransom note itself, while presented as a general advisory, are actually sound security practices.
- Endpoint Protection Platforms (EPP/EDR) for Linux: Solutions like SentinelOne Singularity™ Endpoint and CrowdStrike Falcon offer robust protection for Linux servers, using behavioral AI to detect and stop ransomware before it can encrypt files.
- Strong SSH Security: Disable password-based authentication for SSH and use only key-based authentication. Change the default SSH port and implement fail2ban to block brute-force attempts.
- The 3-2-1 Backup Rule: Maintain at least three copies of your data, on two different types of media, with one copy stored off-site or in the cloud. Test your backups regularly.
- Regular Patching: Keep your Linux distribution, kernel, and all installed software (especially web applications like WordPress, Joomla, and their plugins) up to date to patch vulnerabilities.
- Principle of Least Privilege: Ensure that all services and users run with the minimum level of privileges necessary to perform their tasks.
Post-Recovery: Securing Your Environment and Ensuring Resilience
This critical phase begins after your files have been restored.
- Step 1: Verify Data Integrity and Completeness: Check restored files for corruption and completeness.
- Step 2: Conduct a Full System Scan: Run a full, deep scan of your entire system using a reputable Linux antivirus or anti-malware solution.
- Step 3: Fortify All Credentials: Change all user, admin, service, and cloud passwords. Enforce the use of strong, unique passwords and SSH keys.
- Step 4: Patch and Update Everything: Update the OS and all third-party applications to close security holes that the attackers may have exploited.
- Step 5: Reconnect to the Network Cautiously: Monitor for unusual activity upon reconnection.
- Step 6: Implement or Strengthen a 3-2-1 Backup Strategy: Create or improve a robust backup system and test it regularly.
- Step 7: Perform a Post-Incident Analysis: Review how the attack happened. Use this knowledge to improve security policies and harden systems against a repeat attack.
Reporting Obligations
Report the incident to help combat cybercrime and fulfill potential legal obligations.
- Report to Law Enforcement: In the US, file a complaint with the FBI’s IC3. In the UK, report to Action Fraud.
- Report to CISA: The U.S. Cybersecurity & Infrastructure Security Agency (CISA) urges reporting via its portal.
Conclusion
The Marabu ransomware represents a significant threat to Linux environments, a platform often considered more secure. Its appearance underscores the need for robust security practices on all operating systems. However, like all ransomware, it can be defeated with a calm, methodical, and prepared response. The path to resilience begins long before an attack occurs. Investing in a multi-layered security posture that combines advanced endpoint protection, robust network security, and a disciplined 3-2-1 backup strategy is the most effective defense.
Paying the ransom only fuels the criminal ecosystem and offers no guarantee of a positive outcome. By understanding the tactics of threats like Marabu and preparing accordingly, you can transform a potential catastrophe into a manageable incident, ensuring that your Linux servers—and your critical data—remain secure.
Frequently Asked Questions (FAQ)
Contact Us To Purchase The Marabu Decryptor Tool







3 Comments