SnowSoul Ransomware (.snowsoul) Recovery and Decryption Guide
A new and aggressive ransomware variant, identified as SnowSoul, has been discovered by security researchers. This malware targets both Win32 and Win64 systems, encrypting a wide range of user files. The attackers behind SnowSoul employ a double extortion strategy, combining file encryption with the threat of data leakage, and demand payment in Monero (XMR) for its perceived privacy.
This guide provides a comprehensive, step-by-step playbook for understanding the SnowSoul threat, containing the infection, and exploring every viable pathway to recover your data and protect your organization’s reputation without paying the ransom.
Latest: Marabu (.marabu) Ransomware Recovery and Removal Guide 2025
Threat Summary Table
| Attribute | Detail |
|---|---|
| Threat Name | SnowSoul Ransomware |
| Threat Type | Ransomware, Crypto Virus, Files Locker |
| Platform | Win32, Win64 |
| Encrypted Files Extension | Not specified in the provided note. |
| Ransom Demanding Message | SnowSoul.txt |
| Free Decryptor Available? | No (As of this writing) |
| Ransom Amount | Varies, demanded in Monero (XMR). |
| Cyber Criminal Contact | troyal@tutamail.com, troyal1@tutamail.com, theroyalt@onionmail.org, Discord, Tox. |
| Detection Names | Detected as Win32/Ransom.SnowSoul by some vendors. |
Decoding the Threat: The SnowSoul Ransom Note
The SnowSoul attackers use a text file named SnowSoul.txt to communicate their demands. The note is chaotic and repetitive, a common tactic designed to overwhelm the victim with a sense of urgency and multiple contact points. It emphasizes Monero payments and threatens to publish stolen data globally if the victim does not comply.
The text presented in the ransom note reads as follows:
Just Relax We are Snow Soul All data has been encrypted ---ID: 12494 I am just using this software!!! Do not use Bitcoin addresses Do not attempt to decrypt, file damage, etc. We are not responsible, contact payment - payment will decrypt please pay Monero -!!!! We accept XMR, !!! There is no sky high ransom, can afford it Long term no contact, the key will be automatically deleted (We will publish your data on every black market forum worldwide, and you will bear all consequences on your own) Send your encrypted IP/ID address, write to the following address, and wait for a reply: ↓↓↓↓↓↓↓ troyal@tutamail.com (No reply?) ↓ troyal1@tutamail.com (No reply?) ↓ theroyalt@onionmail.org (No reply?) ↓ discord.com/:@theroyalteam963 github.com/qTox/qTox Download Qtox tox id : 2383E6FB5C55CA86EE55B4A278170EF97A0D2B57FDEDFDBD888B151F9E62EA097429A2461128 Relax I just use this software, note! ! Do not use Bitcoin. All data is encrypted. Please pay in Monero - we accept XMR. Do not attempt to decrypt; we are not responsible for file corruption, etc. Contact us to make payment - decryption will occur upon payment . If there is no contact for an extended period, the key will be automatically deleted. We will publish your data on every black market forum globally, and you will bear all consequences. Send your IP/ID address to the following address and wait for a reply: (ID-12494) ↓↓↓↓↓↓↓ troyal@tutamail.com (Can't contact?) ↓ troyal1@tutamail.com (Can't contact?) ↓ theroyalt@onionmail.org (Can't contact?) ↓ discord.com :: @theroyalteam963 github.com/qTox/qTox Download Qtox tox ID: 2383E6FB5C55CA86EE55B4A278170EF97A0D2B57FDEDFDBD888B151F9E62EA097429A2461128
Indicators of Compromise (IOCs) and Attack Behavior
Recognizing the signs of a SnowSoul infection is the first critical step. The malware’s unique ransom note and its demand for Monero are its most obvious fingerprints.
Indicators of Compromise (IOCs):
- Ransom Note File: The presence of a text file named
SnowSoul.txton the desktop and in folders containing encrypted files. - File Extension: Files will be renamed with a new extension, which was not specified in the provided analysis but will be apparent during the infection.
- Contact Information: The note provides specific email addresses, a Discord handle, and a Tox ID for communication.
- Monero Demand: The explicit demand for payment in Monero (XMR) instead of Bitcoin is a key behavioral indicator.
- Double Extortion Tactic: The explicit threat to publish stolen data on black market forums is a key indicator.
Tactics, Techniques, and Procedures (TTPs) with MITRE ATT&CK Framework:
- Initial Access (TA0001): SnowSoul gains entry through common vectors. These include phishing emails with malicious attachments, exploiting outdated software vulnerabilities, pirated programs, key generators, and malicious ads.
- Execution (TA0002): Once the user executes the malicious file, the ransomware payload is activated, beginning its encryption routine across the system’s drives.
- Impact (TA0040): The primary impact is data encryption. The secondary, and often more damaging, impact is data exfiltration for double extortion, threatening to publish sensitive data if the ransom is not paid.
The Recovery Playbook: A Multi-Path Approach to Data Restoration
This core section outlines the primary methods for recovering your encrypted data.
Path 1: The Direct Decryption Solution
The most direct path to recovery is using a tool specifically designed to reverse the encryption.
Our Specialized SnowSoul Decryptor
Our team has developed a specialized decryptor to counter the SnowSoul threat. By leveraging advanced cryptographic analysis and pattern recognition, our tool can often reconstruct the decryption keys without needing to interact with the attackers.
Step-by-Step Guide:
- Step 1: Assess the Infection: Confirm the presence of the
SnowSoul.txtfile and identify the new file extension. - Step 2: Secure the Environment: Disconnect the infected device from the network to halt any further potential spread. It is critical to remove the malware from your system first.
- Step 3: Submit Files for Analysis: Send a few encrypted samples (under 5MB) and the ransom note file to our team. This allows us to confirm the SnowSoul variant and build an accurate recovery timeline.
- Step 4: Run the SnowSoul Decryptor: Launch the tool with administrative privileges. The decryptor connects securely to our servers to analyze encryption markers and file headers.
- Step 5: Enter the Victim ID: The unique ID provided in the ransom note (e.g.,
12494) is required to generate a customized decryption profile. - Step 6: Automated File Restoration: Once initiated, the decryptor verifies file integrity and restores data automatically.
Public Decryption Tools and Repositories
If our tool is not applicable, several public initiatives are invaluable. Always identify the ransomware strain before using any tool, as running the wrong decryptor can cause permanent damage.
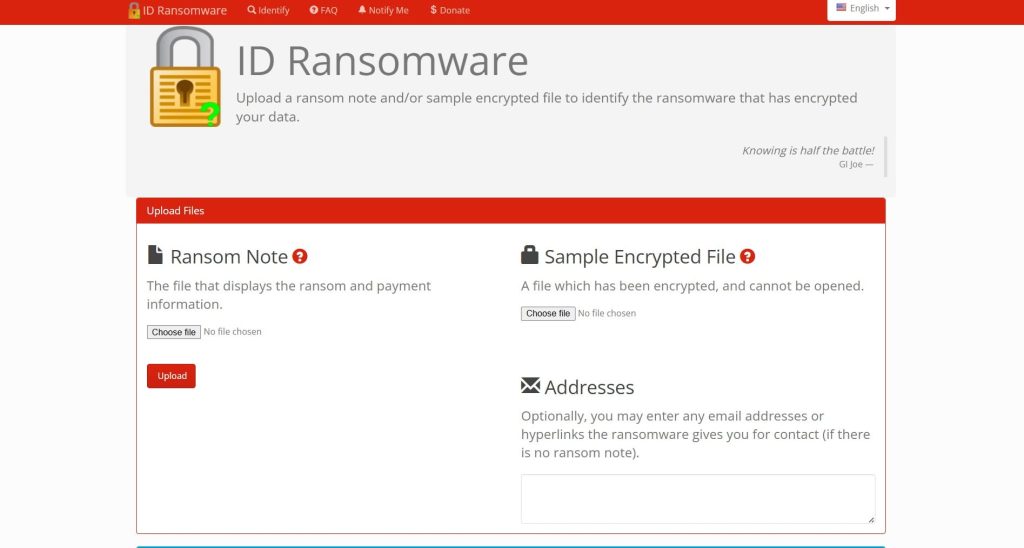
- ID Ransomware Service: Use the free ID Ransomware service to upload the ransom note and a sample encrypted file. The service will identify the strain and tell you if a known decryptor exists. Find it at ID Ransomware.
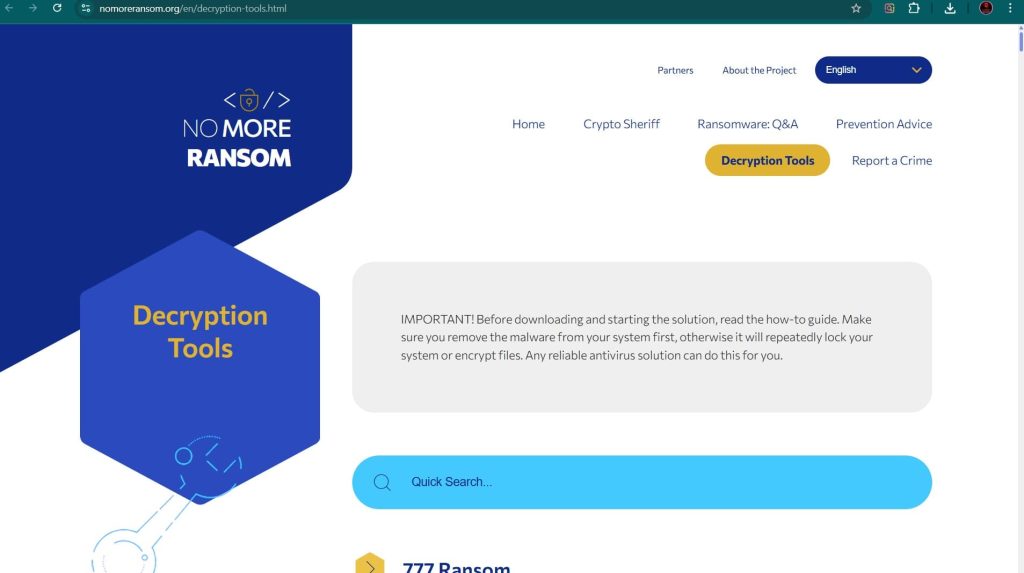
- The No More Ransom Project: This is the most important resource, providing a centralized repository of free decryption tools. Visit their Decryption Tools page and search for “SnowSoul”.
- Major Security Vendor Decryptors:
- Emsisoft: Renowned for its ransomware expertise, Emsisoft offers a variety of decryptors. Check their website for available tools at Emsisoft Decryptors.
- Kaspersky: Through its No Ransom portal, Kaspersky provides the latest decryptors and removal tools. Visit Kaspersky No Ransom.
- Avast: Provides numerous free ransomware decryption tools. Find them on the Avast Ransomware Decryption Tools page.
- Trend Micro: Offers a Ransomware File Decryptor for numerous known ransomware families. You can download it from the Trend Micro website.
Path 2: The Gold Standard – Backup Restoration
If a decryptor is unavailable, restoring from a backup is the most reliable method.
Enterprise-Grade Backups: Veeam
For businesses, Veeam is a market leader in backup and recovery solutions, offering robust protection against ransomware. Veeam can create immutable backups that cannot be altered by the ransomware and offers specialized recovery processes like Cleanroom Recovery to prevent reinfection. Learn more at the official Veeam website.

Cloud and Native Backups
- Microsoft OneDrive: If you use OneDrive, you may be able to restore your files using its Version History feature.
- Windows File Versions (Shadow Copies): SnowSoul likely attempts to delete these, but sometimes remnants remain. To check, right-click on an encrypted file, select
Properties, and go to thePrevious Versionstab.
Path 3: Last Resort – Data Recovery Software
This method has a low probability of success with modern ransomware like SnowSoul but can be a lifeline if no backups exist.
- EaseUS Data Recovery Wizard: A user-friendly tool that can recover lost, deleted, or formatted data. You can download it from the EaseUS website.
- Stellar Data Recovery: A powerful recovery application known for its scanning capabilities. Find it at the Stellar Data Recovery official site.
- Recuva: A free and effective tool for recovering deleted files. Download it from CCleaner’s official site.
Important Procedure: Install the data recovery software on a separate, clean computer. Then, connect the infected hard drive to it as an external drive.
Essential Incident Response and Prevention
A full response includes containment, eradication, and future prevention.
Containment and Eradication
- Isolate the Infected System: Immediately disconnect the machine from the network to prevent the ransomware from spreading.
- Remove the Malware: Use a reputable antivirus or anti-malware program to scan for and remove the ransomware executable.
- Change All Passwords: Assume that credentials have been compromised and change passwords for all user accounts, especially administrators, and for any network services or cloud accounts.
Hardening Your Defenses with Modern Protection
- Endpoint Protection Platforms (EPP/EDR): Solutions like SentinelOne Singularity™ Endpoint and CrowdStrike Falcon focus on preventing ransomware by identifying and neutralizing threats using behavioral AI.
- Integrated Cyber Protection: Tools like Acronis Cyber Protect combine a traditional antivirus with integrated backup and recovery.
- The 3-2-1 Backup Rule: Maintain at least three copies of your data, on two different types of media, with one copy stored off-site or in the cloud.
- Employee Training: Conduct regular security awareness training to teach staff how to spot phishing emails and malicious links.
- Patch Management: Regularly patch all systems and software to close vulnerabilities that ransomware can exploit.
Post-Recovery: Securing Your Environment and Ensuring Resilience
This critical phase begins after your files have been restored.
- Step 1: Verify Data Integrity and Completeness: Check restored files for corruption and completeness by opening a sample from different directories and file types.
- Step 2: Conduct a Full, Deep System Scan: Run a full, deep scan of your entire system using a reputable antivirus or anti-malware solution.
- Step 3: Fortify All Credentials: Change all user, admin, service, and cloud passwords. Enforce the use of strong, unique passwords for every account.
- Step 4: Patch and Update Everything: Update the OS and all third-party applications to close security holes that the attackers may have exploited.
- Step 5: Reconnect to the Network Cautiously: Monitor for unusual activity upon reconnection.
- Step 6: Implement or Strengthen a 3-2-1 Backup Strategy: Create or improve a robust backup system and test it regularly.
- Step 7: Perform a Post-Incident Analysis: Review how the attack happened. Use this knowledge to improve user training and security policies.
Reporting Obligations
Report the incident to help combat cybercrime and fulfill potential legal obligations.
- Report to Law Enforcement: In the US, file a complaint with the FBI’s IC3. In the UK, report to Action Fraud.
- Report to CISA: The U.S. Cybersecurity & Infrastructure Security Agency (CISA) urges reporting via its portal.
Conclusion
The SnowSoul ransomware represents a significant threat due to its strong encryption, its demand for privacy-focused Monero, and its aggressive double extortion tactics. However, like all ransomware, it can be defeated with a calm, methodical, and prepared response. The path to resilience begins long before an attack occurs.
Also read: Fusion Ransomware (.fusion) Recovery and Decryption Complete Guide
Investing in a multi-layered security posture that combines advanced endpoint protection, robust network security, and a disciplined 3-2-1 backup strategy is the most effective defense. Paying the ransom only fuels the criminal ecosystem and offers no guarantee of a positive outcome. By understanding the tactics of threats like SnowSoul and preparing accordingly, you can transform a potential catastrophe into a manageable incident, ensuring that your data—and your peace of mind—remain secure.
Frequently Asked Questions (FAQ)
Contact Us To Purchase The SnowSoul Decryptor Tool







3 Comments